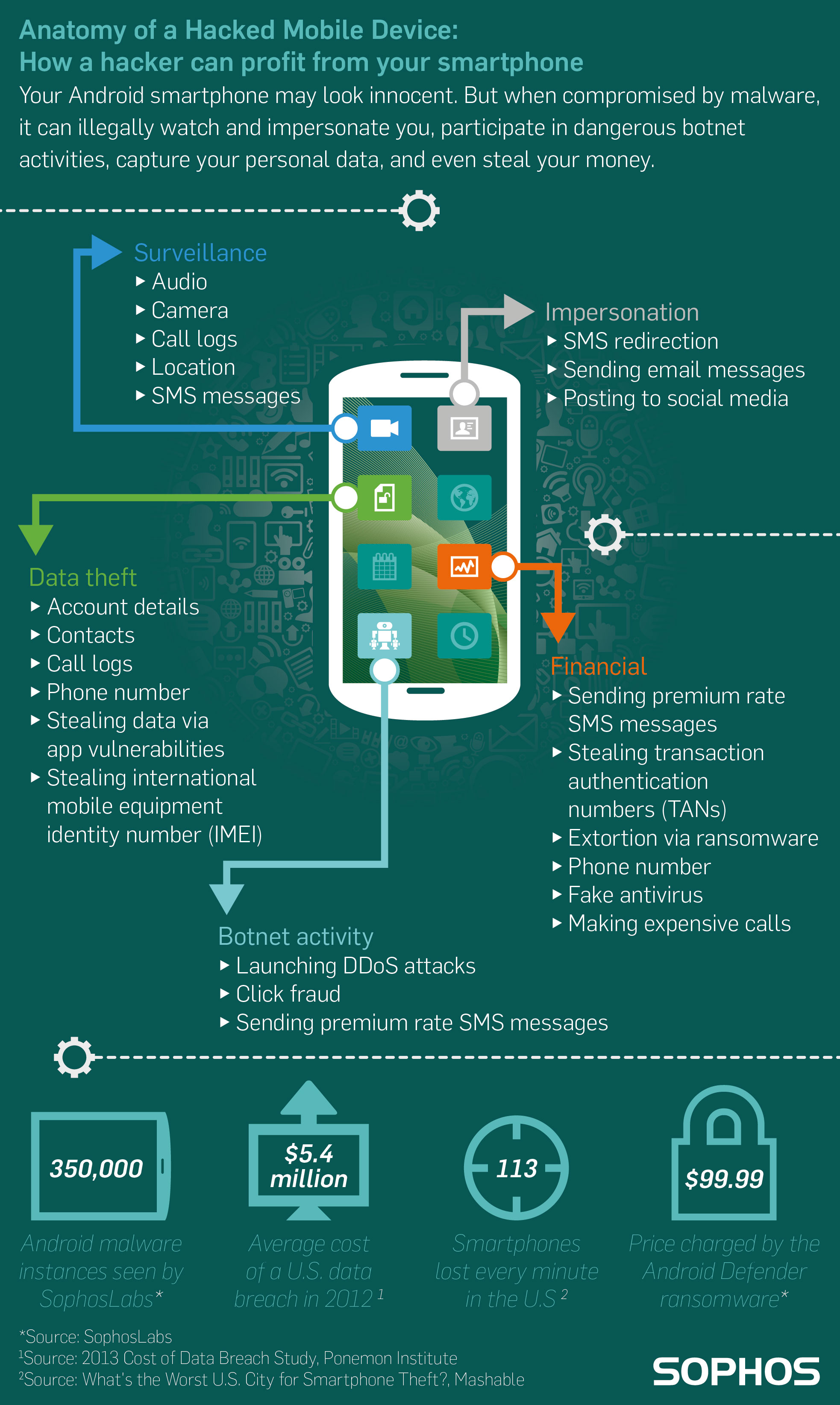
Free Vector | Criminal hacking personal data and stealing money. hacker carrying bag with cash from unlock phone flat illustration.

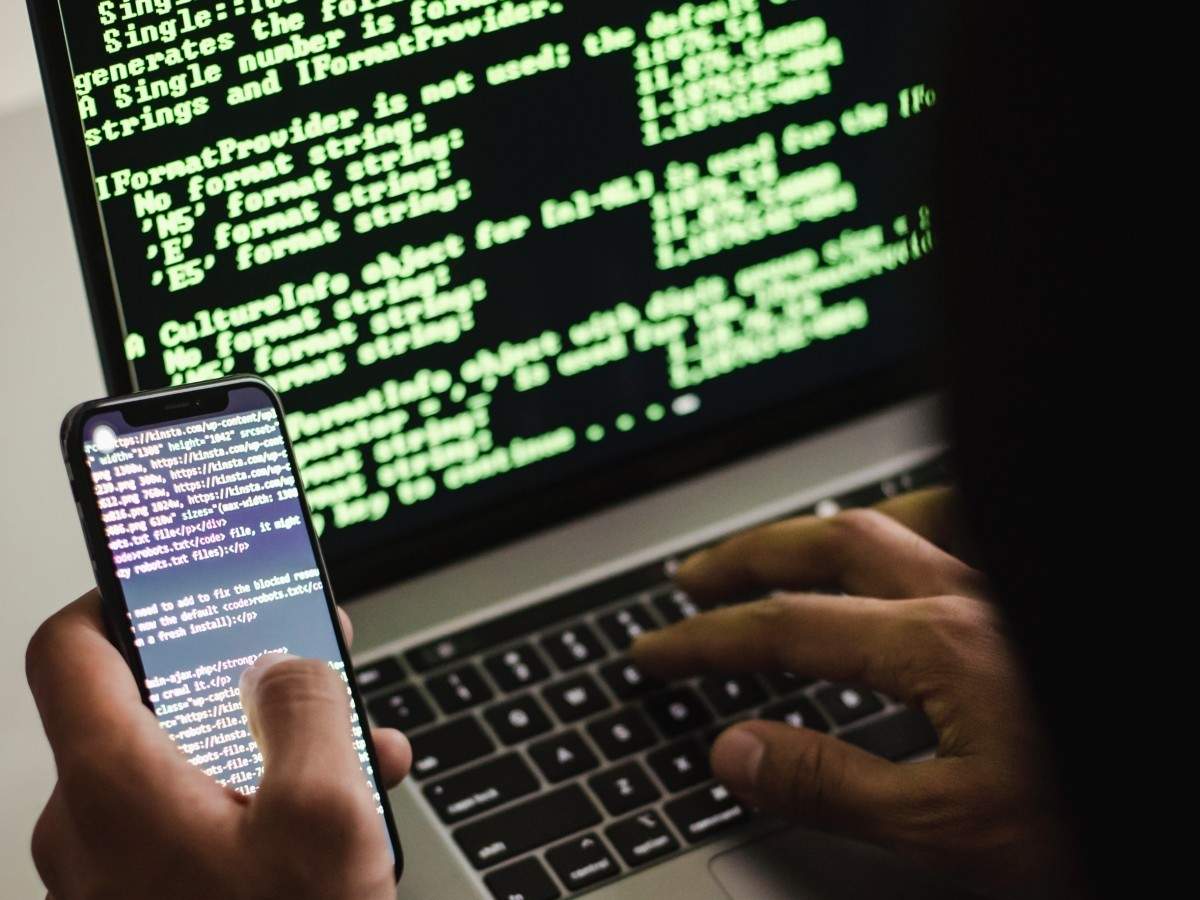
Male Hacker Uses the Mobile Phone To Hack the System. Concept of Cyber Crime and Hacking Electronic Devices Stock Photo - Image of internet, person: 106585664