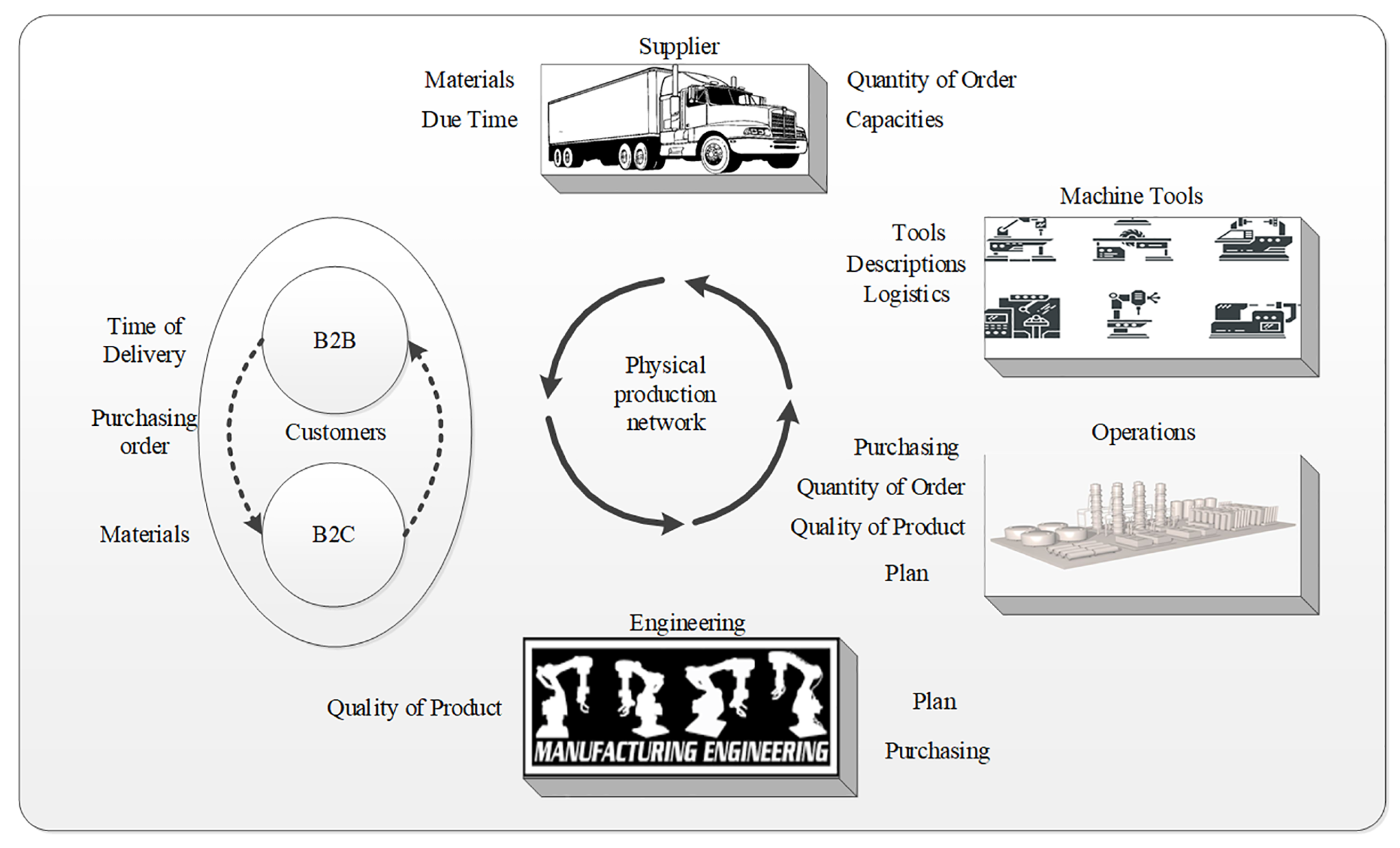
Electronics | Free Full-Text | Supply Chain 4.0: A Survey of Cyber Security Challenges, Solutions and Future Directions

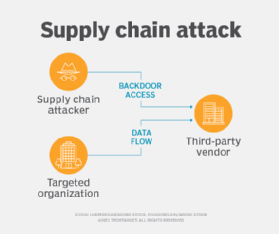
Addressing The Cybersecurity Challenges Of Global Supply Chains - CyberSec4Europe | Cyber Security for Europe
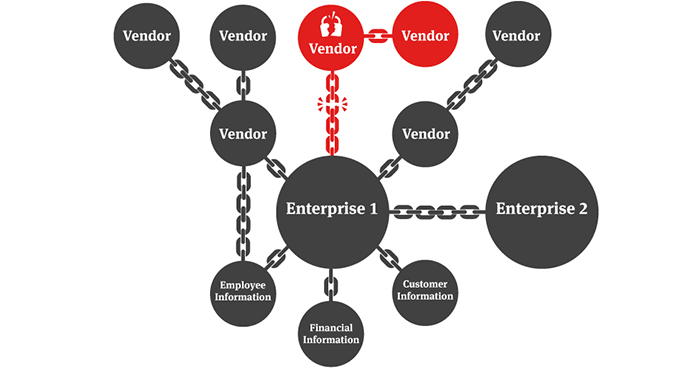
![PDF] Management of Cyber Security Threats in the Factories of the Future Supply Chains | Semantic Scholar PDF] Management of Cyber Security Threats in the Factories of the Future Supply Chains | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f0dec39b6ba3d4b35771e7f55782f0ec17d8c444/3-Figure1-1.png)
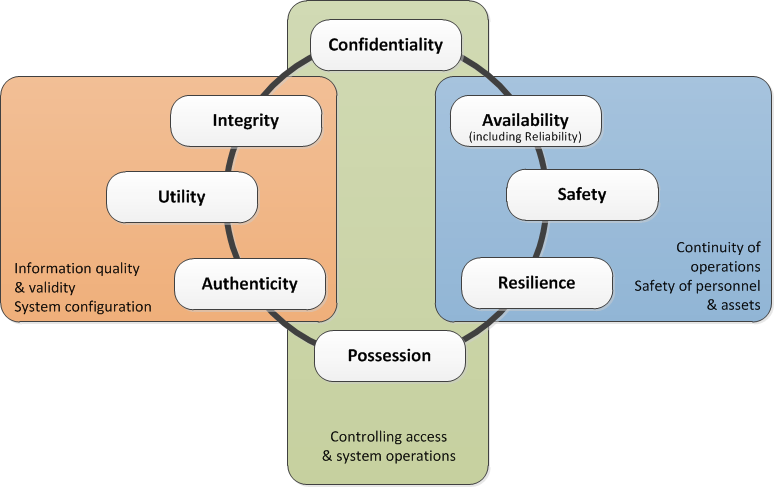
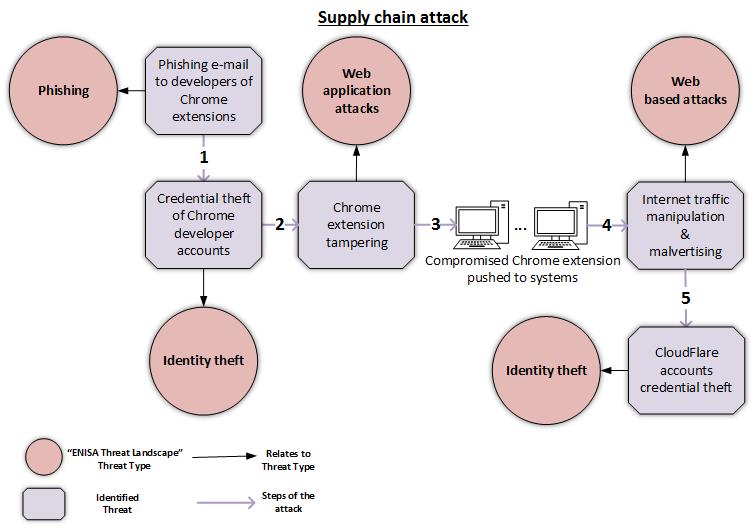
PDF] Management of Cyber Security Threats in the Factories of the Future Supply Chains | Semantic Scholar
Six degrees of separation: cyber risk across global supply chains | United States | Global law firm | Norton Rose Fulbright