GitHub - zenfish/tct: The Coroner's Toolkit, an old-timer's forensic set of tools, written back in the day....

History and Evolution of Computer Forensics Notes - Computer forensics has a long and fascinating - Studocu
Parklane Plowden Podcast - Understanding coroner inquests and the role of lawyers - Parklane Plowden

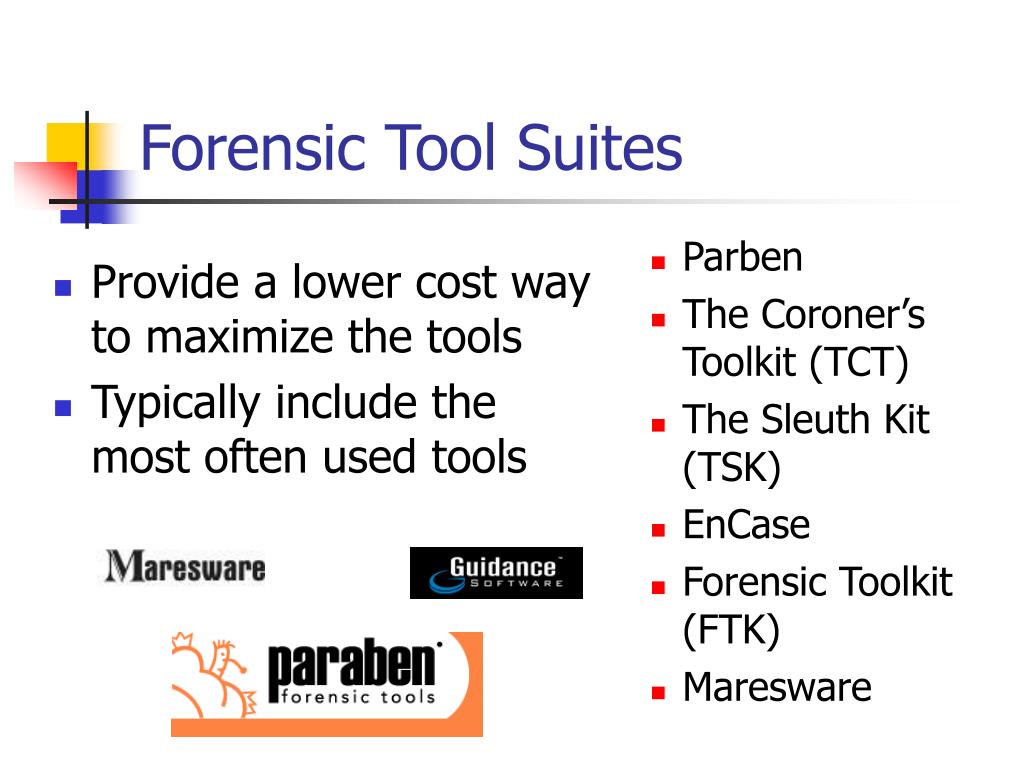
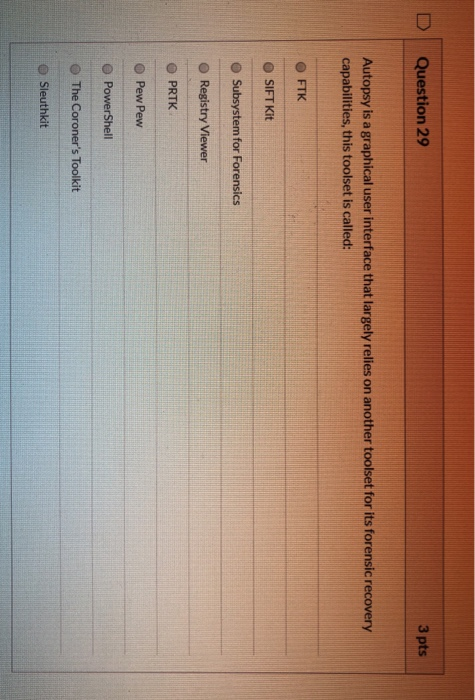
PPT - IMT 3551/4012 Digital Forensics Course Overview and Lecture 1 Fall 2010 PowerPoint Presentation - ID:1931793
SOLVED: Consider the statements below Which forensic tool is being described? Creates a channel of communication between hosts Creates a reliable,TCP connection between the target system and the forensic workstation Has a

CIT 380: Securing Computer SystemsSlide #1 CIT 380: Securing Computer Systems Forensics. - ppt download